Tools used
ImageMagick is a powerfull CLI tool for image processing. For different commands, see their www pages. The following commands are used in this blog:
-
compare
-
convert
-
montage
In addition ImageMagick contains image filters like Laplacian (IM, wikipedia), Sobel (IM, wikipedia) and Prewitt (IM, wikipedia). These filters are also used in steganography.
The hidden, secret, messages are embedded into the original PNG image by using some selected steganographic tools:
ImageMagick contains features to detect edges and to compare images, so it could be used to visualize how the secrect data is distributed over the image. (Naturally hash comparisons would indicated differences, but without showing where they are located)
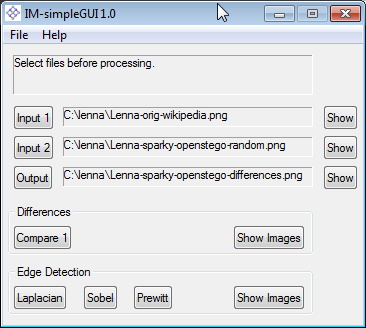
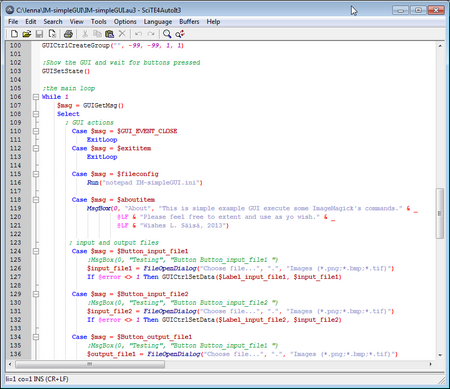
Command line interface is practical for batch processing. However, for casual interactive testing, a GUI alternative can be comfortable. A simple GUI for ImageMagick can be done by AutoIt. The screenshot below shows the GUI made for this particular purpose.
Input Files
Original image is the Lenna 512*512 photo. The photo is widely used test image for processing algorithms.
Files hidden inside the lenna picture:
-
short.txt
-
-
862 bytes
-
text extract from Lenna at wikipedia
-
-
Lenna in Wikipedia.pdf
-
-
62 482 bytes
-
pdf printout from Lenna at wikipedia
-
-
sparky2012.png
-
-
183 125 bytes
-
photo used in earlier blog
-
Result examples
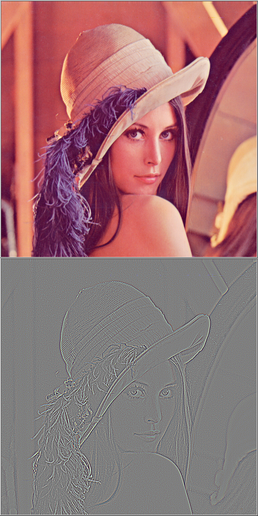
Case 1 Applying filter for edge detection.
The images are: original and the applied Laplacian filter.
Case 2 Hidden Message
File short.txt is encrypted and hidden in original image, starting from the top. The images are: original, modified and the differences. In the differences image, it is visible that only the top part if affected, and the rest of the image is unchanged.
Case 3 Hidden Message
File “Lenna in Wikipedia.pdf” is encrypted and hidden in original image using the Sobel filter. The images are: original, modified and the differences. In the differences image, it is visible that the changed pixels (white) are concentrated at the edges.
IM-simpleGUI tool
The source code is included in the IM-simpleGUI.zip package (hash by FileVerifier++):
- favicon.ico: icon for the GUI
- IM-simpleGUI.au3: the AutoIt based source code
- IM-simpleGUI.exe: the executable compiled by AutoIt tools
- IM-simpleGUI.ini: the main configuration file for the GUI
The tool is provided for learning purposes. It is kind of minimal example on how to develop a GUI for CLI tool.
The source code contains example on howto:
- use ini configuration file
- define tooltip for controls
- define menu structure
- select file
- define tool icon for the GUI
- execute command and capture command output
- use a function
- use console printout for debugging
Example of the Imagemagick commands used in the tool are: (for details, please see source code)
compare -verbose -metric ae -compose Src -highlight-color White -lowlight-color Black C:\lenna\Lenna-orig-wikipedia.png C:\lenna\Lenna-sparky-openstego-random.png C:\lenna\Lenna-sparky-openstego-differences.png
C:\Windows\system32\cmd.exe /c convert C:\lenna\Lenna-orig-wikipedia.png -define convolve:scale='!' -bias 50% -morphology Convolve Laplacian:1 C:\lenna\Lenna-sparky-openstego-differences.png
C:\Windows\system32\cmd.exe /c convert C:\lenna\Lenna-orig-wikipedia.png -define convolve:scale='50%!' -bias 50% -morphology Convolve Sobel C:\lenna\Lenna-sparky-openstego-differences.png
C:\Windows\system32\cmd.exe /c convert C:\lenna\Lenna-orig-wikipedia.png -define convolve:scale='!' -bias 50% -morphology Convolve Prewitt C:\lenna\Lenna-sparky-openstego-differences.png
Note, The tool is provided in order for any modifications and learning. As it is, no support…